The critical value of the Essential Eight security framework
The Australian Cyber Security Centre (ACSC) continues to release an alarming series of alerts about escalating cyber threats. The ACSC recommends Australian organisations should: “urgently adopt an enhanced cyber security posture. Organisations should act now and follow ACSC’s advice to improve their cyber security resilience in light of the heightened threat environment.”
The ACSC encourages organisations to implement ACSC’s flagship security framework – called the Essential Eight. It urges organisations to: “review the Essential Eight and prioritise remediating any identified gaps in Essential Eight maturity.”
A simple, pragmatic and cost-effective cybersecurity approach
For SMBs at the start of their cyber security journey, it can seem like a long, complex and costly road. For many SMBs, it can be difficult to know where to start, and also to know how much cyber security is enough.
That’s where the Essential Eight comes in. It removes a lot of the concern and complexity for customers, because ACSC cyber security experts have done most of the thinking and planning for you. They’ve identified the major threats and listed actions to mitigate them. For cost-conscious SMBs, the good news is the Essential Eight is free expert consultancy.
For partners, the Essential Eight provides an easy-to-follow plan that helps you to identify where your services can quickly and cost-effectively implement baseline security mitigation. Each of the Essential Eight mitigations is a building block on the road to beefing up security.
The Essential Eight mitigation strategies are grouped under 3 major themes:
- prevent attacks (stop malware intruding into your network)
- limit extent of attacks (prevent malware spreading if it does intrude)
- recover data & system availability (backup data and test that data recovery processes work).
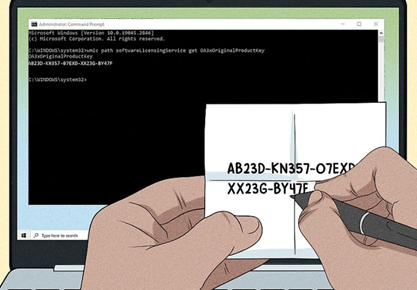
The three major themes and eight mitigation strategies of the Essential Eight are summarised in the table below.
| Theme | Mitigation strategy |
| Prevent Attacks | Application Control
Patch Applications Configure Microsoft Office Macros User Application Hardening |
| Limit Extent of Attacks | Restrict Administrative Privileges
Patch Operating Systems Multi-factor Authentication |
| Recover Data & System Availability | Regular Backups |
The beauty of the Essential Eight is it breaks up all the potential security threats and related mitigations into eight digestible chunks and describes in detail what organisations need to do to strengthen their defences against the threats.
SMBs are given a list of actions and metrics for each of the eight mitigations to reduce their risk from cybercrime. When SMBs implement the recommended security standards for each of the eight mitigation strategies, they start to build a joined-up security strategy.
This can then be used as the SMB’s cyber security roadmap. It serves as an action plan and a security policy document that can be understood and communicated to all staff in the business. And importantly, it can serve as a transparent checklist that business leaders can review to ensure their SMB is taking the right steps to keep cybercrime at arm’s length. The Essential Eight security checklist can also be audited as part of compliance processes.
Get customers started with an Essential Eight Maturity Assessment
The Essential Eight is the outcome of some serious thinking by highly talented ACSC cyber security experts and provides a practical and realistic starting point for many SMBs.
For partners, Crayon has a service offering that can help you get your customers on the right track. Our Essential Eight maturity assessment offering is ideal whether you have an existing cybersecurity practice or need new ways to respond to increased concern from your SMB customers.
Learn More about how we can help.